rsa-al.gov - The Retirement Systems of Alabama
UnitedHealthcare (UHC) and Providence Hospital are currently in contract negotiations.
Security-First Identity Solutions | RSA Cybersecurity
RSA provides identity intelligence, authentication, access & governance solutions, defending the world’s most secure organizations against cybersecurity risks.
RSA cryptosystem - Wikipedia
The RSA (Rivest–Shamir–Adleman) cryptosystem is a family of public-key cryptosystems, one of the oldest widely used for secure data transmission.
RSA Token - Office of Information Technology Services
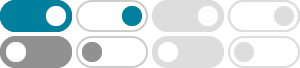
RSA is a multi-factor authentication (MFA) technology that is used to protect network services. The RSA authentication mechanism consists of an assigned hardware or software "token" that generates a …
RSA Algorithm in Cryptography - GeeksforGeeks
Jul 23, 2025 · RSA (Rivest-Shamir-Adleman) Algorithm is an asymmetric or public-key cryptography algorithm which means it works on two different keys: Public Key and Private Key.
What is the RSA algorithm? | Definition from TechTarget
Feb 11, 2025 · What is the RSA algorithm? The RSA algorithm (Rivest-Shamir-Adleman) is a public key cryptosystem that uses a pair of keys to secure digital communication and transactions over insecure …
RSA encryption | Definition, Example, & Facts | Britannica
Dec 18, 2025 · RSA encryption, type of public-key cryptography widely used for data encryption of e-mail and other digital transactions over the Internet. A user secretly chooses a pair of prime numbers …
RSA Public Key Format | Baeldung on Computer Science
Jul 6, 2024 · Learn about the RSA algorithm and different formats that the public key can be stored in.
RSA Encryption: Definition, Architecture, Benefits & Use - Okta
Aug 30, 2024 · RSA allows you to secure messages before you send them. And the technique also lets you certify your notes, so recipients know they haven't been adjusted or altered while in transit. The …
About RSA | The Security-First Identity Leader
RSA provides automated identity intelligence, authentication, access, governance, and lifecycle capabilities to reduce risks, secure authentication, maintain compliance, and automate processes.